Your basket is currently empty!
Coin Afriq Whitepaper
A Pan-African Secure Digital Currency
Andre’ Theron
technical@coinafriq.org
https://coinafriq.org
Abstract. A peer-to-peer version of electronic cash that provides
seamless, near-instant payments without the need for a centralised
financial institution with the goal of a unified digital currency
Across the African continent. By leveraging a distributed public ledger,
Secure next-generation public-key cryptography, network timestamps,
smart contracts and a fair, democratic consensus mechanism called Nominated Proof of Stake on a Byzantine Fault Tolerant network, we can ensure seamless transparent transactions and allow an ecosystem for digital wallets, decentralised applications, and decentralised autonomous communities.
Executive Summary
The problem with leading digital currencies is the high entry barriers for ordinary people. This is especially true in developing regions such as Africa. Furthermore, the leading digital currency (Bitcoin) is computationally expensive and environmentally wasteful. Not only does it use massive electrical utilisation, but for effective participation, high-end machines or dedicated machines (such as ASICs) are required.
Africa is a continent rich in natural resources as well as people and diversity. It boasts a rapidly growing population with increasing demands for financial inclusion. Additionally, Africa is a largely untapped market deterred by minimal financial infrastructure. Africans want participation, greater purchasing power, and sustainable development.
Coin Afriq aims to provide a secure digital currency and ecosystem with technology on-par with, and exceed in some circumstances, existing digital currencies in addition to being environmentally friendly.
By leveraging our technological ecosystem with low economic barriers for entry, a fair and democratic system backed by real-world projects and assets, we can not only foster greater economic development and alleviate wealth inequality but also ensure effective return of investment via increased participation and liquidity.
Massive poverty and obscene inequality are such terrible scourges of our times — times in which the world boasts breathtaking advances in science, technology, industry, and wealth accumulation — that they have to rank alongside slavery and apartheid as social evils.”
—Nelson “Madiba” Mandela, Trafalgar Square London, 2005
1. Introduction
Digital currencies have grown in roughly the last decade and a half. Bitcoin’s initial value relative to traditional currencies was zero. At the time of writing, Bitcoin is valued at roughly R1.5 million. This staggering increase in value and adoption heralded a new age for finance in the digital world. The problems with Bitcoin and similar models are the high initial barriers for entry, environmental waste, and increased centralisation.
Coin Afriq aims to provide a decentralised blockchain and currency built on an already proven industry standard programming language (Rust) that’s not only concurrent and secure but is also rapidly gaining in popularity and is a favourite among developers. This ensures that a new programming language is not needed, thus saving developer time and cost. Our blockchain has a library of smart contracts to automate transactions and validation. These smart contracts are in addition Turing complete in computation – they can essentially run any algorithm, allowing for a wide range of applications.
We also seek to address the problems of centralisation by introducing a variation on the nPoS model referred to as Nominated Proof of Stake (nPoS) – in this system, stake is not the only metric; validator nodes are nominated by another node based on proven rating metrics. This ensures greater participation by a fair and democratic system, not only favouring those with the most stake as collateral.
Furthermore, we have ensured our blockchain is protected against the Byzantine Generals Problem – a problem where some validators may be malicious- by way of providing Byzantine Fault Tolerance (BFT) natively, effectively even if 33% of validators are malicious actors.
In the case of malicious actors, slashing (a method of punishing validators with bad intentions) is used to effectively – a portion of the staked tokens (digital currency) is forfeited, thus ensuring there is no issue of Double Spending.
2. Coin Afriq Blockchain
Our philosophy in building a highly secure, accessible, and decentralised digital currency is to make sure Coin Afriq matches our values set out in our founding, namely:
Security: Because it runs on a public ledger, it must be safe against attacks from malicious agents while respecting user privacy and regulations.
Robustness: Coin Afriq must provide a stable base layer. This is to ensure that we remain decentralised and to minimize attacks.
Scalability: Coin Afriq, while offering innovation, must not be a victim of excessive resource spending in terms of processing, bandwidth, storage, and computational usage.
Applicability: Coin Afriq must address the needs of ordinary people while allowing innovation without reinventing the wheel, leading to excessive development time and resources.
The goal of Coin Afriq in terms of a blockchain is to combine cutting edge technology in security, frameworks, and privacy and improving upon already existing established blockchain concepts such as smart contracts, hashing, public key encryption, and Byzantine Fault Tolerance.
Basing our decentralised ledger system on a proven framework (Iroha2) and a vast interoperable system of frameworks (Hyper ledger), we can ensure the rapid processing of transactions, privacy, and even asset generation that can be done by simply a few lines of code or using a Command Line Interface (CLI).
Besides being technologically sound, we utilise a low initial price per coin, environmentally friendlier participation, and greater democratic control of wealth while offering investors a real-world asset-backing solution, thus ensuring high liquidity for Return on Investment.
3. Market Analysis
Technology use is growing in African countries as developing nations.
Greater internet access, reduced costs of smartphones, and greater adoption of internet-capable hardware lead to an industry ripe with potential. After the COVID-19 pandemic in South Africa, the total online transaction value in digital payments is projected to reach US$19.96 billion this year. The total transaction volume is expected to show an annual growth rate (CAGR 2025-2029) of 29.86%, resulting in a projected total amount of US$56.76B by 2029. This presents a growing opportunity for digital finance to tap into these markets, which service diverse goods from groceries to electronics and luxury goods. This represents a growing market, and similar trends are seen in other African nations, which boast a population of nearly 1.5 billion people.
Our ideal user is the average citizen of an African nation who wants a secure, digital payment solution without the excessive costs normally associated with foreign payments. As we aim to make using our ecosystem as easy as possible, this will be readily accessible for anyone with a capable device (smartphone, computer) and internet access.
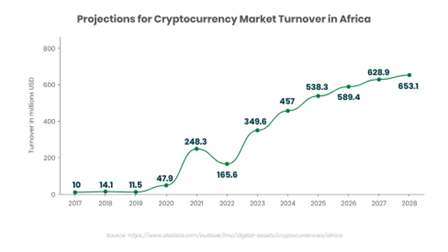
Based on statistics, the African continent’s crypto Total Addressable Market is worth $2.9 Billion.
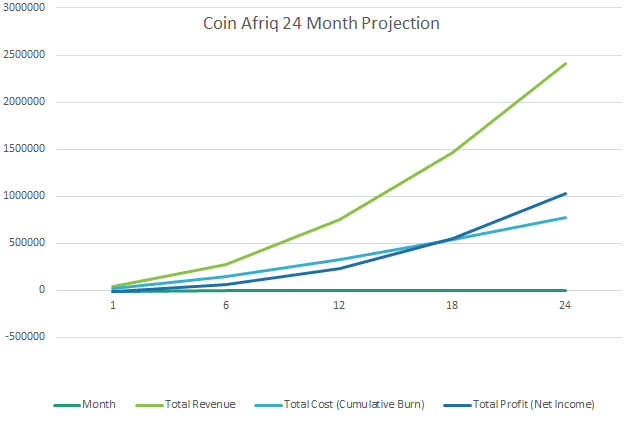
Based on a conservative target, we could conclude a reasonable Service Addressable market of $17.4 Million and thus a good target Serviceable Obtainable Market of $1.74 Million calculated over 24 months.
Our indirect international competitors are strong in their market share; however, because of the high entry barriers, it remains outside the purview of ordinary Africans to buy, sell, trade, or use them as an alternative currency.
Because our initial buy-in is highly affordable there are very low barriers for trade.
One potential threat to the adoption of our ecosystem is the slow adoption of the majority of people to a novel idea like digital currency.
Although digital currency has substantially grown in countries such as Nigeria and cities such as Cape Town in South Africa, many people remain unaware or skeptical due to the proliferation of meme coins – made as a joke and, although sometimes successful, often are highly volatile. A somewhat technical nature of some of the leading digital currencies and their alternatives is the difficulty in purchasing and selling.
To mitigate the problem of lack of awareness, we shall endeavour to educate as many people as possible about this emerging technology via the media (both traditional and social) and advertising and by partnering with leading service providers in the digital finance industry.
To mitigate the problem of scepticism, we remain transparent in all our operations, and because we are backed by tangible real-world projects and assets, this ensures that people know this is an actual financial endeavour.
Finally, addressing the technical proficiency barrier, we not only provide a distributed ledger and digital currency, but also a rich ecosystem including a secure digital wallet (Imali Wallet) – a non-custodial simple wallet that can be used to buy, sell, send and receive Coin Afriq that is accessible, secure, verified and is cross-platform for both mobile (iOS and Android) and desktop users regardless of operating system (Mac OS, Windows and Linux).

4. Tokenomics
Coin Afriq (CAFQ) is the native digital currency powering a cutting-edge blockchain designed to foster economic growth and interoperability across Africa. Built with robust technology including post-quantum cryptography, ISO20022 compliance, and a highly scalable NPoS consensus mechanism, CAFQ is engineered for secure, efficient, and widespread adoption.
4.1. Token Ticker and Name: CAFQ / Coin Afriq
4.2. Total Supply: A fixed total supply of 10,000,000 CAFQ ensures scarcity and long-term value potential.
4. 3. Initial Distribution Strategy:
The initial distribution of CAFQ is strategically designed to foster decentralization, incentivize early adoption, and fund the ongoing development and growth of the Coin Afriq ecosystem.
- Pre-Seed Allocation: An initial allocation will be utilized to fund the development of the Minimum Viable Product (MVP), showcasing the core technological capabilities of the Coin Afriq blockchain.
- Pre-Sale (10%): 1,000,000 CAFQ will be allocated for a pre-sale event targeting early supporters and strategic partners. This phase provides crucial early capital at a discounted price of R6.80 per CAFQ, rewarding early commitment and fueling initial development and marketing efforts leading up to the public launch.
- Initial Coin Offering (ICO) (Up to 15%): Up to 1,500,000 CAFQ will be offered to the wider public during the ICO at a price of R8.50 per CAFQ. This phase aims to broaden token distribution, build a strong community, and secure the necessary capital for scaling the platform, expanding the ecosystem, and pursuing strategic partnerships.
- Foundation/Development Team (20-25%): A portion of the total supply is reserved for the ongoing development, maintenance, and expansion of the Coin Afriq blockchain and its ecosystem. These tokens will be subject to a vesting schedule to ensure long-term alignment with the project’s success.
- Staking Rewards (Initial Allocation) (15-20%): A designated amount of CAFQ is allocated to incentivize early participants in the Nominated Proof-of-Stake (NPoS) consensus mechanism, rewarding those who contribute to network security and stability.
- Community Incentives/Airdrops/Partnerships (5-10%): A portion is reserved for future community growth initiatives, airdrops to increase awareness and adoption, and strategic partnerships to expand the Coin Afriq ecosystem across Africa.
4. Token Utility:
CAFQ is the lifeblood of the Coin Afriq ecosystem, serving multiple critical functions:
- Pan-African Medium of Exchange: Facilitating seamless and low-cost transactions for goods and services across the African continent.
- Transaction Fees: A small network fee of 0.5% is applied to on-chain transactions, a portion of which is allocated to a deflationary burn mechanism and the remainder to network maintenance and validator incentives.
- Smart Contract Gas: Fueling the execution of smart contracts, powering Decentralized Applications (dApps), and enabling Decentralized Finance (DeFi) protocols built on the Coin Afriq blockchain.
- dApp, DeFi, and Derivative Token Fees: A lower fee of 0.2% is applied to transactions within dApps, DeFi platforms, and involving derivative tokens built on the Coin Afriq blockchain, incentivizing ecosystem development.
- Staking and Governance: Enabling holders to participate in the NPoS consensus mechanism by staking their CAFQ to nominated validators and potentially participating in future on-chain governance processes.
- Base Asset for Derivative Tokens: Serving as the foundational currency for the creation and interaction with derivative tokens within the Coin Afriq ecosystem.
5. Deflationary Mechanism:
To enhance the long-term value proposition of CAFQ, a deflationary burn mechanism is implemented. 0.25% of the 0.5% network transaction fees will be systematically burned, permanently removing CAFQ from the total circulating supply. This mechanism aims to increase the scarcity of CAFQ over time, potentially driving value appreciation with sustained or increasing demand. The specific burn rate will be continuously evaluated and may be subject to future governance proposals.
6. Long-Term Vision: Path to Gold Peg:
As the Coin Afriq ecosystem matures and generates sufficient profit from network operations, the long-term vision includes establishing a peg to the value of gold. This ambitious goal aims to provide a stable and reliable store of value for CAFQ holders, further solidifying its position as a trusted Pan-African currency. The specific mechanism for achieving this peg (direct backing, stablecoin model, algorithmic peg) will be determined and communicated to the community in due course, with transparency and security being paramount.
7. Commitment to Growth and Adoption:
The tokenomics of CAFQ are carefully designed to incentivize early adoption, reward network participation, and fuel the long-term growth of a vibrant and interconnected Pan-African digital economy. Through strategic partnerships, a thriving developer ecosystem, and a user-centric approach, Coin Afriq aims to become the leading digital currency for the African continent.
5. Use of Funds
We are specifically looking for investors to invest in our pre-seed phase for the goal of launching an MVP of our product. Our aim is a value of $300 000 to account for:
- MVP Development
- Operational Foundation and Early Traction
- Strategic Pre-Sale Marketing and Community Building
- Securing Future Liquidity and Visibility through Strategic Partnership
- Contingency and Exchange Rate Buffer
Our project has a strong technical foundation, a clear path to market (we have a great listing agency), an experienced team and strategic alliance, a concrete roadmap to liquidity in sight and focused execution and de-risking.
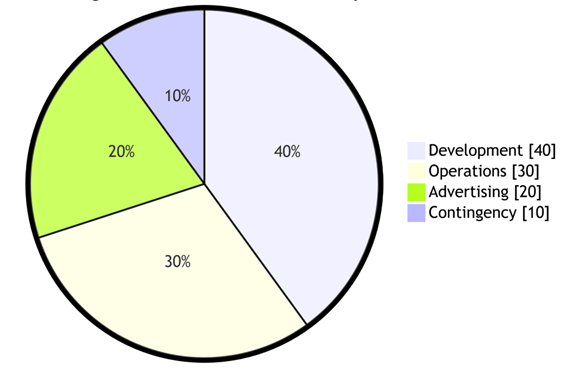
Funds from pre-seed will be allocated in the following manner:
- Development (40% – $120 000) – for building a robust MVP
- Operations (30% – $90 000) – to establish a strong foundation
- Marketing (20% – $60 000) – to generate early traction
- Contingency (10% – $30 000) – ensuing project stability
We will provide investors access to all our books, which will be checked and audited. We have already approached seasoned professionals in bookkeeping, accounting, and auditing to assist us.
6. Technical Design
6.1 Technical History
The concept of the decentralised currency is not new at all. In the early 1980s, various alternative currencies were proposed, and attempts were made toward implementation. Unfortunately, while these currencies had (at the time) acceptable security protocols and privacy measures, they were plagued by the reliance on a centralized intermediary. In 1998, b-money was introduced as a concept by Wei Dai. This had a decentralised consensus and would be one of the inspirations behind Bitcoin’s PoW model. Unfortunately, Wei Dai’s proposal was not feasible due to having legible details.
Hal Finney, later in 2005, introduced the concept of “reusable PoW”. This concept was fused with Adam Back’s Hash cash puzzles, difficult to solve puzzles that are encrypted.
However, due to technological limitations and a reliance on (then) trusted computing back ends, this fell short of goals.
Another issue that plagued early digital currencies was due to the important anonymity, the contemporary security protocols were prone to Sybil Attacks – a single malicious actor would create thousands of nodes on a server, or by using bots, and steal a majority share.
The first cryptocurrency was a radical new change in security, finance, and commerce.
BitCoin was started by a person named Satoshi Nakamoto, who introduced two novel concepts. First was the BitCoin (BTC), a novel, secure, peer-to-peer (P2P), decentralised online currency that is not staked against traditional or fiat currency and maintains a consistent value. This was issued without a central bank or political state using a secure decentralised public ledger commonly referred to as the blockchain.
Per the experiment of Satoshi, the concept of Proof of Work (PoW) was introduced as a system to verify transactions based on public agreement. BitCoin worked based on a file-to-system system – if entity A sends n amount of BitCoin to entity B, only the transaction that gets confirmed first will process.
The genius behind Satoshi Nakamoto’s blueprint was a simple decentralised consensus mechanism and high-tech security. By combining transactions into a block pattern every ten minutes on a scalable blockchain and using security algorithms and a PoW mechanism, it allows individual nodes to gain the right to participate by solving complex mathematical puzzles. This implementation, while revolutionary, was not without faults. Larger computational power led to greater influence and reward for nodes used by individuals that could afford it, creating a problem that as Bitcoin grew, it was only viable for users with the finances to support either multiple high-end computers or ASIC machines. Users without as much economic privilege decided to join mining pools. Mining Pools, unfortunately, lead to more centralisation, which in turn leads to Mining Pools or Mining Farms essentially controlling all the rewards. In addition, as complexity increased for solving blocks, the PoW not only proved computationally expensive but environmentally taxing, leading the Vice-Chair of the European Securities and Markets Authority to call for a ban on PoW models in favour of PoS.
A new digital currency was later invented on a platform called the Ethernet Blockchain, using their native digital currency called Ether (ETH). Its novel utilising smart contracts and multiple uses of the decentralised ledger and distributed database initially also used a PoW model. While this addressed some issues of BitCoin, such as the determination of time-based transactions, it was also built on the Proof of Work (PoW) model, leading to high electrical usage.
On the 15th of September 2022, Ethereum moved to a traditional PoS model. This event was referred to in the community as The Merge. This decision, although with a minority of detractors, led to the Ethereum network lowering its energy consumption by 99%.
Ethereum also introduces novel concepts to the model of the digital currency, namely smart contracts, systems that automatically facilitate the transfer of digital assets according to arbitrary predefined rules. It also demonstrated that the blockchain could be used for more than just currencies.
Digital decentralised applications (Apps) could be built and the blockchain could be used for Fungible Tokens (such as digital currency), Non-Fungible Tokens (such as digital artwork, copyright, etc.) reputation systems and even Decentralised Autonomous Organisations – digital democracies that can contain laws, bylaws, agreements and assets of an entire community or organisation.
The problem that has plagued Ethereum was the use of the Proof of Work model, however, Ethereum decided to transition to a Proof of Stake model (PoS). While this was beneficial in reducing the burden of high environmental cost and ensured that Ethereum was more accessible to anyone in part due to not requiring highly advanced computer systems or specialised machines to “mine” the blocks in the blockchain, it also led to a problem of centralisation. Under the traditional Proof of Stake (PoS) model, validators are chosen based on the amount of ETH they already have to stake.
While indeed those who stake a lot of their digital assets stand to lose them if acting maliciously, it also created a new entry barrier. With the price of ETH already being high, thanks to successful exchange, few people could afford the 35 ETH requirement to stake. In addition, when a few large players dominate the validation process, it increases the probability of censorship, 51% attacks, and the Byzantine Generals Faults.
6.2 Transactions
A digital currency is defined as an asset, usually a coin that is fungible and uses a chain of digital signatures. Each coin owner transfers their coin to the next owner by digitally signing a hash of the previous transaction and adding their encrypted public key.
The subsequent owner can verify the signatures to verify the claim of ownership.
Traditionally, in its infancy, there was no way to verify that a transaction wasn’t a victim of double spending. To mitigate this, we have developed using open source code and frameworks and use a decentralised public ledger that is available on a global P2P network often referred to as the Mainnet.
With Coin Afriq, we use “transactions” to refer to an externally signed data package that stores a message to be sent. Transactions contain the recipient of the message, a signature identifying the sender, the amount of Coin Afriq, and the data to be sent.
To offset network costs, we charge a transaction fee that will be used to maintain the network and also an amount that will be used for reward to validators and nominators in our Nominated Proof of Stake (nPoS) system as outlined later in this paper.
Our proposal and development include Special Instruction triggers that may be invoked on condition. This is a very powerful feature and enables Turing complete computation. This is generally divided into three categories:
- Trigger at timestamp
- Trigger at blockchain
- Trigger at condition
These categories ensure that data must have previously existed at a time, on the blockchain and/or a specialised condition, to get into the hash. In the case of timestamps, each timestamp includes the previous timestamp in its hash; this, in turn, forms a chain with each subsequent timestamp reinforcing the ones before it.
6.3 Smart contracts
A smart contract is a computer program or transaction protocol that is intended to automatically execute, control, or document events and actions according to the terms of a contract or agreement. This allows us to have a reduction of need for trusted intermediaries, arbitration costs, and fraud losses, in addition to the reduction of malicious and accidental exceptions. This technology was proposed by Vitalik Buterin, author of the Ethereum whitepaper, in 2014. Besides the above-listed benefits, it allows room for innovation and growth by way of a building block toward decentralised finance (DeFi) and non-fungible tokens (NFT) applications, as well as a system of bylaws for decentralised autonomous communities (DAO).
Besides these advantages, a benefit is a zero-cost Foreign Function Interface. Intrinsic functions that are implemented on our platform directly are callable by programs. Calling these functions will suspend the program and schedule the function on a high-performance server. Intrinsic functions are batched together to execute in parallel on the Graphics Processing Unit (GPU). An example of this would be the Elliptic Curve Digital Signature Algorithm (ECDSA) verification. By executing on the GPU, throughput is increased exponentially.
Using the Iroha2 framework, a library of smart contracts is provided based on Special Instructions. To execute logic on the ledger, these transactions can be invoked via either transactions or registered triggers, as noted above in the section on transactions.
Our decision to use this framework is because of interoperability between different Hyper ledger technologies and being based on Rust, which offers built-in memory safety, concurrency, and data safety while offering high speeds due to Rust being compiled to machine code and not having garbage collection.
6.4 Nominated Proof of Stake (nPoS)
Traditional Proof of Stake (PoS) is far more efficient than the Proof of Work (PoW) consensus mechanisms. To begin with, it relies on minimal processing power being able to be used on a variety of platforms, from mobile phones to desktop computers, while also being environmentally friendlier. Bitcoin, the original digital currency, often requires specialised equipment to validate transactions.
The problem however in the standard PoS model in comparison to PoW is that it is prone to centralisation – validators with large holdings can have undue influence on transaction verification; it is not as proven in terms of security as PoW systems; and some digital currencies require locking up staked coins for a minimum amount of time.
To combat this, we have decided on a Nominated Proof of Stake (nPoS) consensus mechanism. The benefits of an nPoS system combat the issue of centralisation by ensuring that both reputation and stake are factors in selecting validators for transactions by ensuring validator nodes are nominated by another node.
This consensus mechanism operates on the Phragmen election technique to ensure fair representation. We divide the network into two primary participants: validators and nominators. Each block is processed by an active validator set. This group of validators is chosen by the nominators. Nominators can nominate a specific number of validator nodes.
After this, validators receive slots in the validator set relative to the stake backing them.
There are four basic roles for participants – the aforementioned validators and nominators, in addition to assistants and whistle-blowers.
6.4.1 Validators
A validator is the highest charge on Coin Afriq and helps seal new blocks on the Coin Afriq network. The validator is chosen based on reputation and a sufficiently high bond, often referred to as stake. Validators are nominated by way of looking at their reputation – track record, on-chain ID, websites, and supporting links. This due diligence is important as validator actions directly affect the nominator’s stake. Validators who receive the most nominators, and thereby have a higher stake backing, become the validators for that block. This changes periodically at a predefined time (known as an era) ranging from 4 to 24 hours. Once the active set is finalised, the network distributes the stake between all chosen validators to keep the process fair.
6.4.2 Nominators
A nominator is any stake-holding party that contributes to the stake of the validator and elects trusted validators. They have no other roles besides placing risk capital as a way of electing nominators they believe will be trustworthy and will act responsibly in the maintenance of the network.
We ensure a pro-rata increase or reduction in their deposit according to the stake’s growth to which they contribute, thus ensuring incentive. There are similar in some ways to mining pools in PoW blockchains.
6.4.3 Assistants
Assistants are similar to transaction collators in other networks – parties who assist validators in producing valid blocks. They retain all necessary information to author new blocks and execute transactions similar to miners on PoW blockchains. Usually, they will collate and execute transactions to create an unsealed block and provide it together with zero-knowledge proof to the validator(s) presently responsible for proposing a new block. At the early stage, we expect assistants to work very closely with validators as during launch there will be lower transaction volume compared to growth.
At the growth stage, additional infrastructure will be put in place due to the cost of maintaining a synced version of the aforementioned block increases.
This, in turn, will help separate the duties to independent, profit-seeking parties. As with transaction collators, we predict that there will be collator pools that compete to collect transaction rewards.
Individual assistants may, however, create a market offering blocks in return for a competitive share of the reward payable immediately. Decentralised nominator pools can allow multiple stakers to assist and share the duties of a validator(s). This ensures further decentralisation and open participation.
6.4.4 Whistle-blowers
Whistle-blowers, people in the real world who reveal information about illegal, unethical, illicit, unsafe, or fraudulent activity, are independent actors who volunteer to watch for illicit and malicious activity and actors on the network. Incentivised by large one-off rewards. Due to this contingency measure, we seldom expect to see real malicious activity. In most cases, it would be due to carelessness, an individual being careless with proper security procedures such as relieving a secret key.
For whistle-blowers to earn their reward of a stake, they must submit timely proof that at least one staking party acted maliciously. Examples of these acts would include helping to ratify an invalid block or double-signing. To prevent over-rewarding or revealing the compromising session’s secret key, the base reward providing a validator’s illegally signed message is minimal.
The reward will increase, however, if corroborating illegal signatures from other validators are reported and can be provided, as this implies a genuine attack. As our network is Byzantine Fault Tolerant in case of 33% malicious actors, we can assert roughly 66% of validators act benevolently.
There are similarities between to what other blockchains refer to as “full nodes” as minimal resources are required and stable uptime and high bandwidth are not a requirement. The difference lies in that Whistle-blowers must post a small stake. This is to protect against Sybil Attacks that could waste validators’ time and resources. Rewards are immediately available to withdraw, no more than a small amount of South African Rand, yet may lead to a hefty reward if genuine malicious validators are reported.
As is standard practice, we utilize slashing as a penalization protocol, wherein stake can be lost for both nominators and validators. For initial unintentional failures, we withhold the validators’ reward. Repeated failures result in the reduction of their security bond.
Demonstrably malicious actions such as double-signing or an attempt to provide an invalid block will result in the loss of the entire bond (utilising slashing, while most is distributed to the informant and honest actors). By combining this with the aforementioned smart contracts, we can ensure a fair system that is Turing Complete.
6.5 Design Overview
6.5.1 Consensus
Coin Afriq achieves low-level consensus over a set of mutually agreed valid blocks by utilising a natively asynchronous Byzantine Fault Tolerant algorithm. As with other implementations, this would be wholly sufficient for Proof of Authority (PoA) style networks. Our goal, however, is to be deployable as a network that is fully open to the public without needing specific organisation or trusted authority for maintenance.
6.5.2 Proof of Stake
Most networks have mechanisms in place to measure how much stake any particular account has. This is usually a unit of measurement often referred to as a token – in our case, an amount of digital currency (Coin Afriq).
We predict in most cases that validators will be elected infrequently through the NpoS consensus mechanism, as outlined above. Incentives for validators and operations through pro-rata allocation of funds from token base expansion.
It can be argued that monetary token base expansion can lead to inflation; however, as all token holders will have a fair opportunity at participation, no Coin Afriq holder would have a reduction in the value of their holdings as long as they are happy to take a role in the consensus mechanism. A specific minimum amount of tokens will be required to stake; the token base expansion is adjusted through a market-based mechanism to reach the target.
As validators are bonded by their stakes, we ensure that exiting validators’ tokens remain in place for a determined period after their duties cease.
This long bond-liquidisation time also allows future malicious actions to be punished up until the periodic checkpoint. Negative actions are punished through reduction of reward, or in severe cases, the validator losing some or all of their stake to other validators, whistle-blower’s or stakeholders as a whole via burning e.g. a validator who engages ina short-range attack (ratifying both branches of a fork) can be identified and punished via burning.
Long-range attacks – where a malicious actor attempts to take over a blockchain with a false chain- are a theoretical threat. For example, a malicious actor starts with the genesis block of the blockchain, including having a significant stake of the token balance higher than the forging balance, and then starts to deceive nodes by creating their branch of the chain, indistinguishable from the real chain.
Long-range attacks usually comprise one of the three different methods:
- Simple
- Posterior Corruption
- Stake Bleeding
It must be noted that although long-range attacks have never been successfully performed on the blockchain, it still must be mitigated against. To combat this, we use the aforementioned validator selection mechanisms and Byzantine Fault Tolerance. Where indeed malicious actors are found, we use punishment methods as previously outlined. For improved detection, we implement checkpoints – snapshots of the blockchain at specific points in time, ensuring that any attempt to modify the blockchain before that point is easily detected and rejected by the network.
6.6 Staking protocols
6.6.1 Staking contract
This contract maintains the validator set. The following parameters are used for management:
- Which accounts are currently validators
- Which accounts are available to become validators at short notice
- Which accounts have placed stake nominating a validator
- Properties of the staking amount, payout rates, addresses, and session identities
Because we allow open participation on a public ledger, this allows an individual to register as a bonded validator (with requirements); it also allows existing validators to exit this status. This also includes mechanisms for validation and canonicalization.
6.6.2 Stake-token Liquidity
It is normally desirable to have as high as possible total staking tokens to be staked, as this allows increased market capitalisation of the staking token as well as aiding network security. However, this also poses a problem – if a token is locked in the Staking Contract under punishment of reduction, how can we have a viable portion remain sufficiently liquid to ensure price discovery?
A solution proposed is a derivative contract securing fungible tokens on an underlying staked token. The problem with this approach is that not only is it difficult to implement in a trust-free manner, but also, derivative tokens cannot be treated equally due to the risk of assets failing, thus becoming worthless. With staked tokens, if a validator acts maliciously, they will be punished.
The best solution to this problem is to ensure that not all tokens are staked. Some portion of the tokens will be set aside to remain liquid. While this might not be ideal in terms of implementation cost, it is the simplest solution and has no probable effect on the security of the network. The vast majority of bond-confiscations will still be able to be used to make reparations possible.
The ratio between staked and liquid tokens can be calculated by simply using a reverse auction mechanism. Token holders interested in being validators can post an offer to a staking contract with a minimum payout rate they require to participate.
At the start of each session scheduled regularly, the validator slots will be filled according to the stake and payout rate. A method of doing this would be to take those with the lowest offers who have a stake no higher than the total stake targeted divided by the amount of slots and no lower than the lower bound of half that amount.
If the slots cannot be filled, we can reduce the lower bond recursively by a specified factor to satisfy the requirements.
6.7 Security architecture
Current digital currencies are generally thought of as being hard to hack.
However, a highly skilled hacker, a group of hackers, or an organisation (whether legitimate, illicit, or state actor) could break through the security protocols of both Bitcoin and Ethereum. Both rely on an elliptic curve key algorithm called Secp256k1 – a Koblitz curve over a prime field for transaction signing.
While indeed at the time of release of Bitcoin, this was cutting-edge technology, technological growth has progressed in the last decade and a half, and cryptography is no exception.
The main problem with Secp256k1 is that it is vulnerable to side-channel attacks. It also relies heavily on the proper generation of the random value k. Poor randomness is vulnerable to private key recovery, as has been demonstrated in real-world attacks. The reason for this can be summed up as :
d=s1k−z1r(modn)d = \frac{s_1k — z_1}{r} \pmod{n}d=rs1k−z1(modn)
Where:
- s1s_1s1 is the signature component.
- z1z_1z1 is the hash of the message m1m_1m1.
- rrr is shared between all signatures with the same kkk.
To achieve better security and improve speed and efficiency, we opted for a newer standard called Ed25519 – a Curve25519 with a twisted Edwards curve.
Not only is this less vulnerable to the aforementioned attacks due to using deterministic signing over random k, its hash function is a newer SHA-512 key over Secp256k1’s older Keccak-256 hashes. While this increased key size might lead people to think it will be slower, real-world examples have shown it is not only faster signature generation and verification. In addition, like Secp256k1, the key size remains 256 bits; it also has 128-bit security while maintaining a key size (32 bytes) similar to Secp256k1’s (33 bytes compressed, 65 bytes uncompressed).
For other security considerations, inside of the hashing of sensitive information with the SHA-2 standard like other networks, we have opted for SHA-3, the latest standard specifically SHA3-512. This requires no additional modification to implement as the National Institute of Standards and Technology (NIST) in the US specifically released SHA-3 to be a drop-in replacement for SHA-2. The other benefit is that while not currently an issue, SHA-2 is not considered secure against quantum attacks. Because SHA-3 relies on Sponge Construction (where data is “absorbed” into the sponge then the result is “squeezed” out) instead of Merkle-Damgard Construction (which uses MD-compliant padding to create an input whose size is the multiple of a fixed number), this is considered to be a quantum resistant hash algorithm.
6.7.1 Solving Quantum Cryptography Concerns
The vast majority of cryptocurrencies and blockchains are in danger of a new looming threat on the horizon – Quantum Computing. While Quantum Computing offers amazing advances in computing and will push our understanding of science ahead by leaps and bounds, in terms of cryptography it offers a huge risk
Shor’s algorithm, a quantum algorithm for integer factorization, exhibits a super-polynomial speedup over the best-known classical algorithms. 1 Given an integer N, the algorithm efficiently finds its prime factors in O((logN)3) time and O(logN) space on a quantum computer. 2 This capability poses a significant threat to the security of widely used public-key cryptosystems, such as RSA and ECC, whose security relies on the computational intractability of factoring large integers and the discrete logarithm problem, respectively. The successful implementation of Shor’s algorithm on a sufficiently large and fault-tolerant quantum computer would render these currently secure cryptographic methods vulnerable to efficient decryption. 3
Leading cryptocurrencies are studying this threat, but have made no certain terms to implement a solution that’s both performant and secure. The National Institute of Standards and Technology recently released their recommendation for a Post Quantum Cryptography as Federal Information Processing Standard (FIPS) 203. This has been standardized as ML-KEM (Module Lattice Based Key Encapsulation Method). This algorithm is secure against both traditional and future quantum computers.
We propose to use a hybrid approach and combine both ML-KEM and ES25519 for maximum security and a for smooth transitioning.
By using ML-KEM-1024 (which is the highest security level offering security comparable to AES-256) and ES25519, we can use ML-KEM-1024 for key exchange (secure communication, shared secrets, etc.) while using ES25519 for transaction signing and verification. This approach ensures very high security while maintaining performance, as ES25519 is already well optimized and modern CPUs can effectively handle ML-KEM-1024. Because our blockchain is programmed using Rust, this improves performance and naturally is a good fit due to Rust’s memory safety, performance and concurrency.
Besides the security of the network, we have opted in the Imali Digital Wallet to enforce multi-factor authentication (two-factor being required, three factor being recommended) in addition to ensuring a strong mnemonic instead of the traditional password is used and to avoid the pitfalls of pen and paper, a requirement is to back it up to the device’s native cloud system (Apple iCloud or Google Drive).
For an additional layers of security, we suggest using a standard mnemonic of 12 to 24 words from a publicly known wordlist to generate our seed value. However, instead of directly using this seed value, we also add a passphrase that is at least 12 characters long using a mix of uppercase, lowercase, numbers and symbols. For seed derivation we use PBKDF2 and Argon2 for encrypting the mnemonic for storage. This encrypted value will be the one store to the device’s native cloud system.
The benefit of this is an increase in security due to the added passphrase.
This seed value is also fully compatible with modern HD wallets using BIP-32.
6.8 Interoperability
A great feature of using Hyperledger Iroha2 is that it natively is highly interoperable with other networks, which is a standard feature using in more blockchains in modern times.
However, very few cryptocurrencies offer support for ISO20022 – a standard used by banks internationally that is increasingly used. We plan on implementing ISO20022 from the MVP stage.
We plan on implementing this by embedding ISO-20022 complaint metadata within the transactions involving our cryptocurrency. We can further use our Smart Contracts for to validate and automatically process ISO-20022 data elements. For serialization and deserialization, we have made the architectural decision to JavaScript Object Notation (JSON).
An added benefit is as we have the capability for dApps, DeFi and derivative tokens, this offers added standardization for these features in terms integration, compliance, asset representation, compliance and regulation.
8. Scalability Planning
Because networks can grow exponentially with new users, our network needs a robust, secure, and scalable system. Our proposal to offset network resource costs is to use sharing – essentially splitting the blockchain into many independent pieces spread out over the peer-to-peer network. Fortunately, this is relatively easy to do with our smart contract system and can be done automatically at network administration parameters. By effectively partitioning the network into smaller shards, having each shard process its transactions and smart contracts and distributing it via decentralisation on a high number of nodes, reducing the burden on individual nodes. The benefits of this include:
- Increased transaction speed – transactions can be processed in parallel.
- Reducing load – reducing the load on individual nodes
- Improving scalability – offsetting heavy network resources
For further scalability, we plan with growth and investment to implement second-layer networks – blockchain protocols built on top of the Layer-1 blockchain. Scaling is a problem normally on any blockchain due to increasing traffic. By leveraging an extra layer, we can have the extra layer do most of the primary work of the blockchain and then send it back to the primary channel.
The combination of these two technologies ensures that the network can handle a large amount of transactions with additional speed and cost efficiency.
9. Roadmap
Our roadmap outlines the strategic phases for the development, launch, and expansion of the Coin Afriq ecosystem. We are committed to transparency and will provide regular updates on our progress.
Phase 1: Foundation & MVP Development (Currently in Progress)
Key Objectives:
- Finalize core blockchain architecture leveraging Rust and HyperLedger Iroha2.
- Complete development and internal testing of the Minimum Viable Product (MVP) showcasing:
- Core transaction functionality with CAFQ.
- Implementation of post-quantum cryptography (ML-KEM and ES25119).
- Demonstration of Byzantine Fault Tolerance.
- Basic wallet functionality.
- Initial showcase of smart contract capabilities.
- Establish core team and operational infrastructure.
- Secure strategic early partnerships.
Phase 2: Pre-Sale & Community Building
- Key Objectives:
- Launch and execute the pre-sale event for early supporters and strategic investors (10% of total CAFQ supply at R6.80 per CAFQ).
- Actively engage and grow the Coin Afriq community through dedicated channels.
- Expand marketing and awareness campaigns.
- Finalize legal and regulatory frameworks for initial launch.
- Secure initial partnerships for ecosystem integration.
Phase 3: ICO & Mainnet Launch (South Africa Focus)
- Key Objectives:
- Conduct the Initial Coin Offering (ICO) for the wider public (up to 15% of total CAFQ supply at R8.50 per CAFQ).
- Successfully launch the Coin Afriq Mainnet.
- List CAFQ on a Tier 2 Centralized Exchange (CEX) with a dedicated market maker focused on liquidity.
- Drive initial user adoption and transaction volume within South Africa.
- Onboard early dApps and DeFi projects to the platform.
- Implement the initial network transaction fee structure (0.5% with burn mechanism).
Phase 4: Building Towards Gold Pegging
- Key Objectives:
- Focus on generating sustainable revenue from network operations within the South African market.
- Strategically explore and establish partnerships within the mining sector, leveraging the founder’s expertise, to secure consistent access to gold resources.
- Research and develop the specific mechanism for pegging the value of CAFQ to gold (direct backing, stablecoin model, etc.), prioritizing security and transparency.
- Begin accumulating initial gold reserves based on operational profits and strategic acquisitions.
- Develop transparent and auditable systems for managing and verifying gold reserves.
Phase 5: Gold Peg Implementation & Initial African Expansion
- Key Objectives:
- Officially implement the gold-pegging mechanism for CAFQ, communicating the details and benefits to the community and potential users.
- Initiate strategic expansion into 2-3 key neighboring African markets, leveraging the enhanced trust and stability offered by the gold peg.
- Focus on early user acquisition and establishing use cases within these initial expansion regions.
- Continue growing the developer community and the number of dApps and DeFi solutions on the platform, highlighting the stability of CAFQ.
Phase 6: Broader Pan-African Expansion & Advanced Features
- Key Objectives:
- Broader expansion across the African continent, adapting strategies for diverse markets, now with the added advantage of a gold-backed currency.
- Focus on large-scale partnerships with businesses, financial institutions, and potentially governments, emphasizing the stability and store-of-value proposition.
- Implement advanced features such as derivative token support and enhanced interoperability.
- Evaluate and potentially pursue listing on Tier 1 Centralized Exchanges, leveraging the credibility of the gold peg.
- Further refine and optimize the network fee structure and burn mechanism based on usage and community feedback.
Our commitment is to build a robust, secure, and widely adopted digital currency that empowers individuals and businesses across Africa. By strategically prioritizing the establishment of a gold-backed peg, we aim to provide unparalleled stability and trust to our users as we expand our reach across the continent. This roadmap outlines our journey, and we look forward to sharing our progress with the community.
10. Conclusion
“What counts in life is not the mere fact that we have lived. It is what difference we have made to the lives of others that will determine the significance of the life we lead.”
—Nelson “Madiba” Mandela
Coin Afriq is more than just a cryptocurrency; it is a vision for a digitally empowered Africa, built on a foundation of robust technology, strategic partnerships, and a commitment to long-term value. Our journey, guided by a phased and deliberate roadmap, begins with a powerful and secure blockchain, designed for the unique needs and opportunities of the African continent.
We are building beyond fleeting trends, establishing a digital currency with the ambition to become a stable and trusted cornerstone of the African financial landscape. Our commitment to exploring a gold-backed peg underscores our dedication to providing a reliable store of value in a dynamic market.
The growing African digital economy presents a fertile ground for innovation, and Coin Afriq is poised to be a key enabler, fostering seamless transactions, empowering local businesses, and connecting communities across borders. With a strong team, a clear strategy, and the support of our growing community, we are confident in our ability to execute our vision and deliver a truly transformative solution.
We invite you to join us on this exciting journey as we build the future of finance in Africa – a future where digital assets empower progress and prosperity for all. Together, we can forge a golden future for the African digital economy, one CAFQ at a time.